Infrastructure as Code: Architectural Implications
Picture this: You’re deploying infrastructure at 3 AM, clicking through AWS console tabs, SSH’ing into servers, manually updating firewall rules. Three weeks later, no one remembers what was changed. This is the pre-IaC world—and it’s a nightmare that still haunts many production systems.
Infrastructure as Code (IaC) isn’t just about automation. It’s a fundamental architectural shift that transforms infrastructure from ephemeral manual configurations into versioned, testable, reproducible artifacts. But this transformation brings profound architectural implications that most teams discover the hard way.
The State Paradox: Your Infrastructure’s Memory Problem
Here’s what nobody tells you: IaC tools maintain a “state file”—a snapshot of what infrastructure exists. This state becomes your system’s single source of truth, but it’s also your biggest liability. Netflix learned this when a corrupted Terraform state file during a deployment left hundreds of instances in an undefined state—neither fully created nor destroyed.
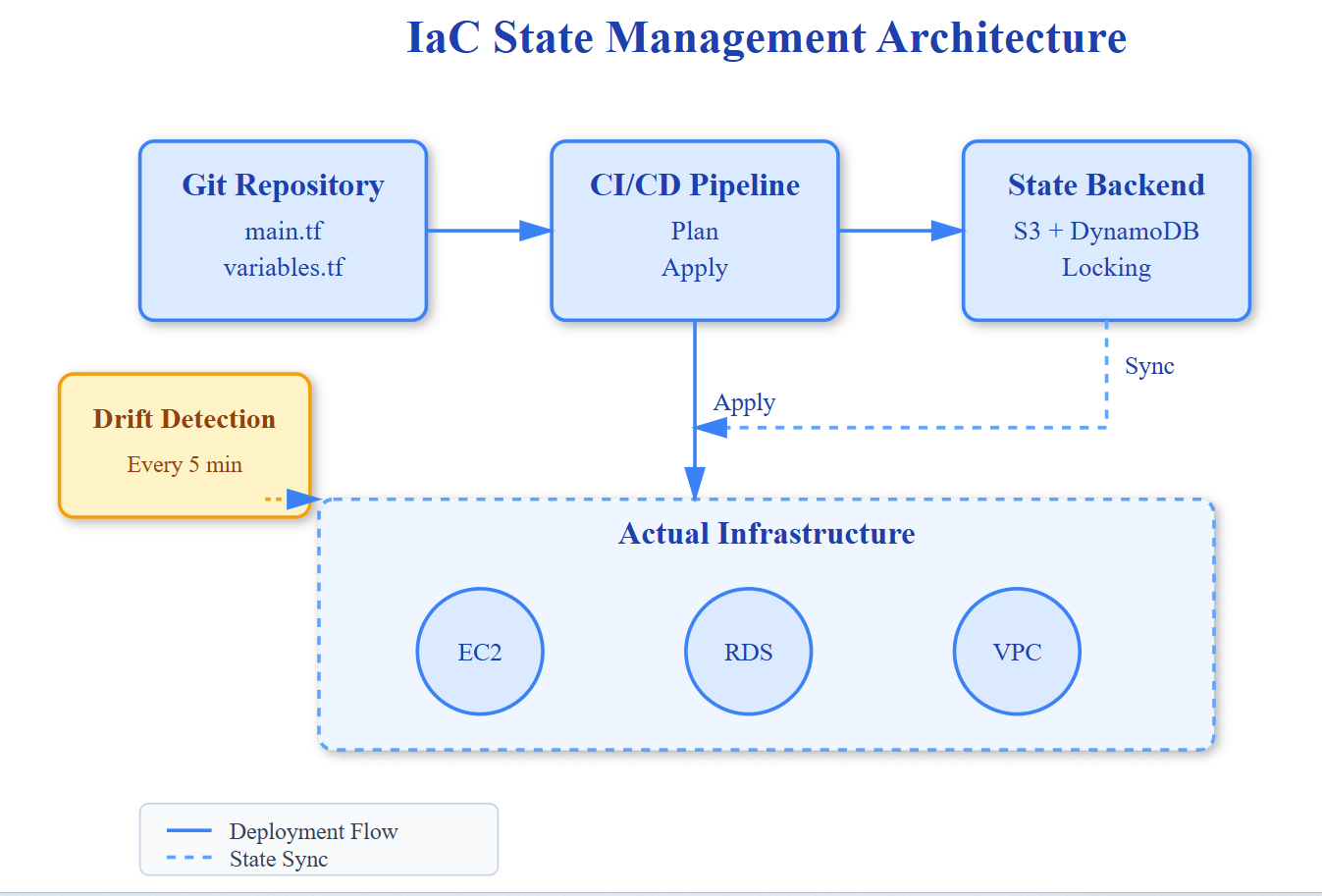
The architectural implication: your deployment pipeline must treat state files as critical as your production database. They need backup strategies, locking mechanisms (preventing concurrent modifications), and disaster recovery plans. Stripe runs state files through distributed consensus (using DynamoDB for Terraform) because losing state is worse than losing a database—you lose the ability to know what you own.