Multi-Tenant System Architecture Patterns
What We’ll Master Today
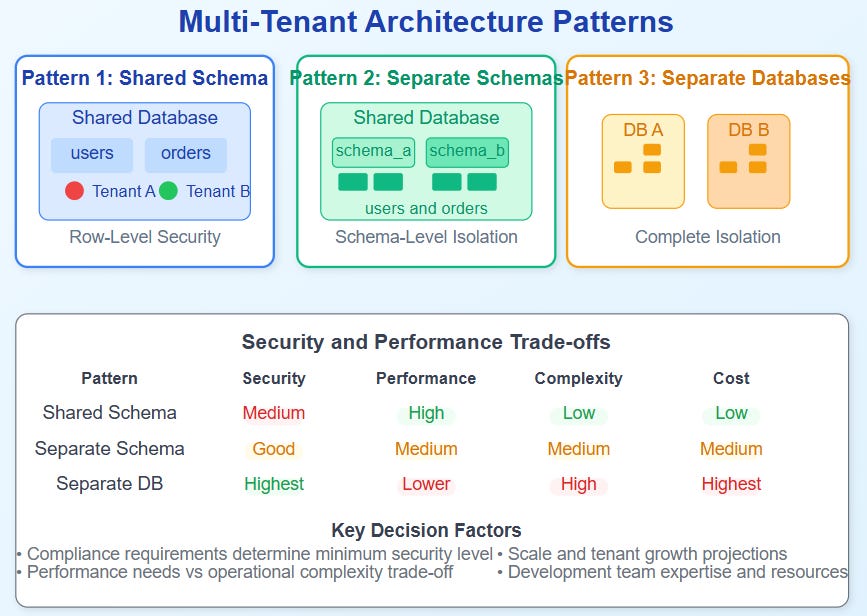
Tenant Isolation Strategies: Database-per-tenant vs shared schemas with row-level security
Performance Optimization Patterns: Connection pooling, caching, and resource allocation across tenants
Security Boundaries: Cross-tenant data leaks prevention and access control mechanisms
Scaling Challenges: Noisy neighbour problems and elastic resource distribution
The $47 Million Data Leak That Changed Everything
When Salesforce accidentally exposed one customer’s data to another in 2019, the incident cost them $47 million and fundamentally shifted how the industry thinks about multi-tenant architecture. The leak happened not through a sophisticated attack, but through a simple query that crossed tenant boundaries during a routine database maintenance operation.
This wasn’t just a security failure—it revealed the hidden complexity of building truly isolated multi-tenant systems. Today, we’ll explore the architectural patterns that prevent such disasters while maintaining the cost efficiency that makes SaaS profitable.
The Three Pillars of Multi-Tenant Architecture